

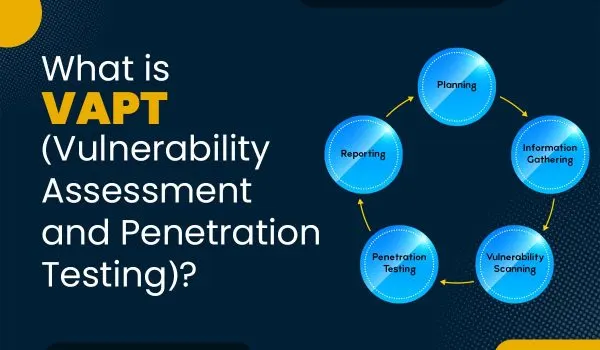
VAPT stands for Vulnerability Assessment and Penetration Testing. It is a security testing process designed to identify, evaluate, and help fix weaknesses in an organization's IT systems, applications, or network.
Vulnerability Assessment involves scanning and identifying known security flaws in the system. This step provides a list of potential vulnerabilities without actually exploiting them.
Penetration Testing (or ethical hacking) takes it a step further by safely attempting to exploit the discovered vulnerabilities, just like a real attacker would. This helps determine how dangerous the flaws actually are and what kind of damage they could cause.
We provide highly customized solutions tailored to your specific business logic, using a balanced approach that combines both manual and automated testing.
Here's an overview of how we carry out IT security penetration testing.

Detailed information about the devices, network architecture, and protocols in use is obtained.

Detailed information about the devices, network architecture, and protocols in use is obtained.

Detailed information about the devices, network architecture, and protocols in use is obtained.

Detailed information about the devices, network architecture, and protocols in use is obtained.

Detailed information about the devices, network architecture, and protocols in use is obtained.
Detailed information about the devices, network architecture, and protocols in use is obtained.
Detailed information about the devices, network architecture, and protocols in use is obtained.

Detailed information about the devices, network architecture, and protocols in use is obtained.

Detailed information about the devices, network architecture, and protocols in use is obtained.
© Cyber defentech is Proudly Owned by Cyber defentech