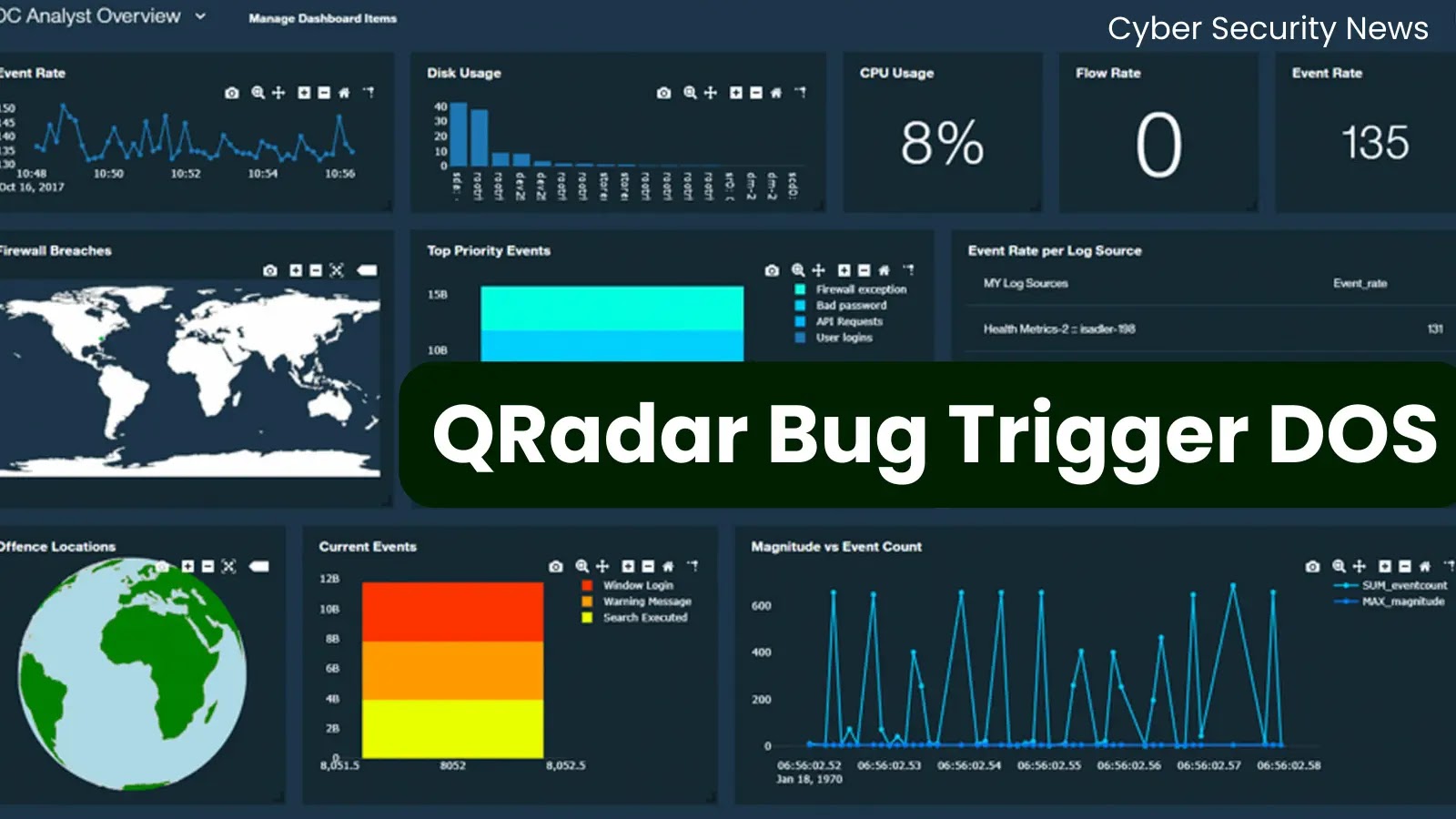
QRADAR: IBM TOOL
IBM QRadar is a Security Information and Event Management (SIEM) solution that provides comprehensive, real-time threat detection and response capabilities by aggregating and analyzing data from various sources across an IT infrastructure. Designed to meet the security needs of modern enterprises, QRadar helps organizations detect and investigate security incidents, providing an in-depth understanding of network …
READ MORE