CLOUD SECURITY
Secure cloud environments & applications.



We proactively detect potential cyber risks before they impact your business, ensuring stronger defense and faster response.

We evaluate your digital infrastructure to uncover vulnerabilities and reduce potential cyber risks.

Testing in cyber security identifies and fixes system vulnerabilities to protect data and ensure security.

We secure your cloud infrastructure with advanced monitoring and controls to protect data and applications.



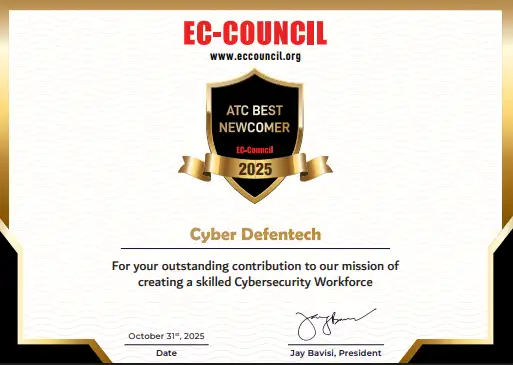
Your Roadmap to Educate, Excel, Empower



Robust measures to protect databases from breaches, ensuring confidentiality, integrity, and availability of data.

Comprehensive protection of IT systems against unauthorized access, vulnerabilities, and cyber threats.

Safeguarding websites and web applications from attacks, data breaches, and unauthorized access.

Protecting servers from cyber threats, ensuring safe data storage, uptime, and reliable performance.
© Cyber defentech is Proudly Owned by Cyber defentech